Önceliğimiz
güvenliğiniz
forms.app tasarım itibari ile güvenlik ve gizlilik dostudur. Burada, aldığımız teknik önlemleri ve verilerinizi nasıl güvende tuttuğumuzu inceleyebilirsiniz.
Dünya çapında güçlü markalar forms.app’e güveniyor
Sertifika ve uyumluluklar
forms.app verileri nerede depolar?
Spam koruması
forms.app’te hesap güvenliği
Form gizliliği
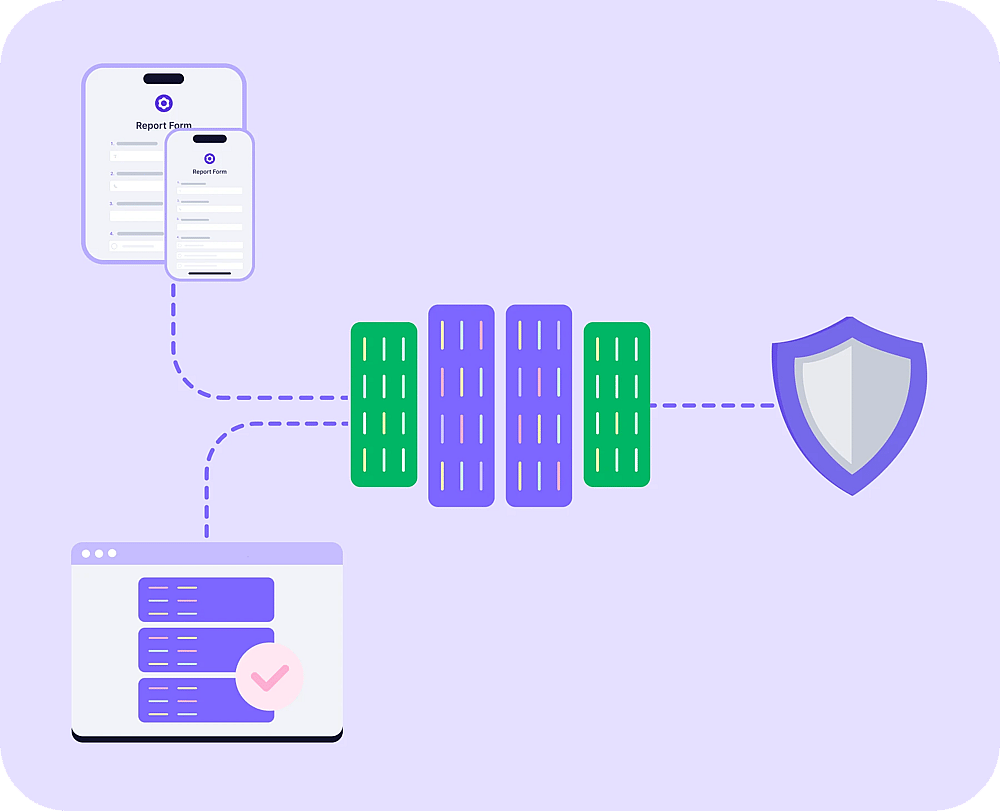
Altyapı ve ağ güvenliği
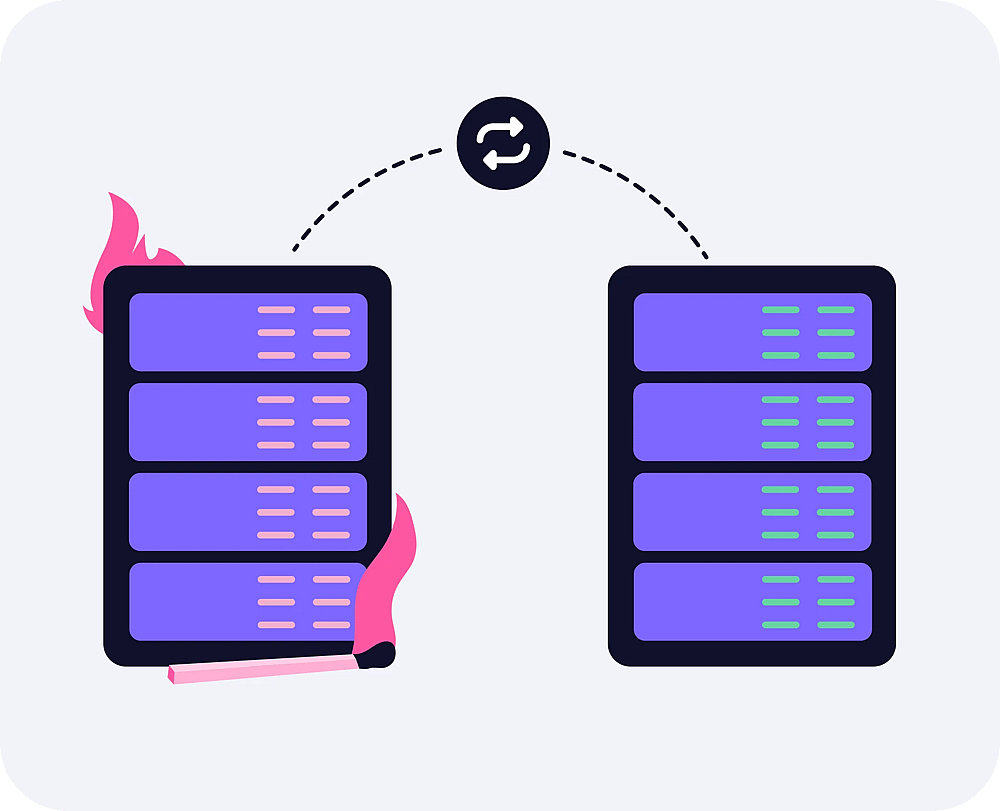
Acil durum kurtarma
Çalışan güvenliği
Hata ödül programı
Ek kaynaklar
Güvenlik önlemleri hakkında daha fazla bilgi
The measures to ensure confidentiality include;
1.1. Physical Access Control;
Measures suitable for preventing unauthorized persons from gaining access to data processing systems with which personal data are processed or used.
a. Technical Measures
- Automatic access control system
- Biometric access barriers
- Smart cards
- Manual locking system
- Doorbell system with camera
- Video surveillance of entrances
b. Organizational Measures
- Reception / Receptionist / Gatekeeper
- Employee / visitor badges
- Visitors accompanied by employees
- Care in selection of cleaning services
- Information Security Policy
- Work instructions for operational safety
- Work instruction access control
1.2. Logical Access Control;
Measures suitable for preventing data processing systems from being used by unauthorized persons.
a. Technical Measures
- Login with username+strong password
- Firewall
- Intrusion Detection Systems
- Use of VPN for remote access
- Automatic desktop lock
- Encryption of notebooks / tablet
- Two-factor authentication in data center operation and for critical systems
Organizational Measures
- User permission management
- Creating user profiles
- Central password assignment
- Information Security Policy
- Work instruction IT user regulations
- Work instruction operational security
- Work instruction access control
- Mobile Device Policy
1.3. Authorization Control;
Measures to ensure that those authorized to use a data processing system can only access the data subject to their access authorization and that personal data cannot be read, copied, modified or removed without authorization during processing, use and after storage.
a. Technical Measures
- Logging of accesses to applications, specifically when entering, changing, and deleting data
- SSH encrypted access
- Certified SSL encryption
b. Organizational Measures
- Use of authorization concepts
- Minimum number of administrators
- Management of user rights by administrators
- Information Security Policy
- Work instruction communication security
- Work instruction Handling of information and values
1.4. Separation Control;
Measures that ensure that data collected for different purposes can be processed separately. This can be ensured, for example, by logical and physical separation of the data.
a. Technical Measures
- Separation of productive and test environment
- Physical separation (systems / databases / data carriers)
- Multi-tenancy of relevant applications
- VLAN segmentation
- Staging of development, test and production environment
b. Organizational Measures
- Control via authorization concept
- Determination of database rights
- Information Security Policy
- Data Protection Policy
- Work instruction operational security
- Work instruction security in software development
1.5. Pseudonymization;
The processing of personal data in such a way that the data can no longer be attributed to a specific data subject without the use of additional information, provided that such additional information is kept separately and is subject to appropriate technical and organizational measures.
a. Technical Measures
- log files are pseudonymized at the request of the client
b. Organizational Measures
- Internal instruction to anonymize/pseudonymize personal data as far as possible in the event of
- disclosure or even after the statutory deletion period has expired
- Information Security Policy
- Data Protection Policy
- Specific internal regulations on cryptography
The measures to ensure integrity include;
2.1. Transfer Control;
Measures to ensure that personal data cannot be read, copied, altered or removed by unauthorized persons during electronic transmission or while being transported or stored on data media, and that it is possible to verify and establish to which entities personal data are intended to be transmitted by data transmission equipment.
a. Technical Measures
- Use of VPN
- Logging of accesses and retrievals
- Provision via encrypted connections such as sftp, https and secure cloudstores
- Use of signature procedures (case dependent)
b. Organizational Measures
- Survey of regular retrieval and transmission processes
- Transmission in anonymized or pseudonymized form
- Careful selection of transport personnel and vehicles
- Personal handover with protocol
- Information Security Policy
- Data Protection Policy
2.2. Input Control;
Measures that ensure that it is possible to check and establish retrospectively whether and by whom personal data has been entered into, modified or removed from data processing systems. Input control is achieved through logging, which can take place at various levels (e.g., operating system, network, firewall, database, application).
a. Technical Measures
- Technical logging of the entry, modification and deletion of data
- Manual or automated control of the logs(according to strict internal specifications)
b. Organizational Measures
- Survey of which programs can be used to enter, change or delete which data
- Traceability of data entry, modification and deletion through individual user names (not user groups)
- Assignment of rights to enter, change and delete data on the basis of an authorization concept
- Retention of forms from which data has been transferred to automated processes
- Clear responsibilities for deletions
- Information Security Policy
- Work instruction IT user regulations
The measures to ensure availability and resilience include;
3.1. Recoverability Control;
Measures capable of rapidly restoring the availability of and access to personal data in the event of a physical or technical incident.
Technical Measures
- Backup monitoring and reporting
- Restorability from automation tools
- Backup concept according to criticality and customer specifications
Organizational Measures
- Recovery concept
- Control of the backup process
- Regular testing of data recovery and logging of results
- Storage of backup media in a safe place outside the server room
- Existence of an emergency plan
- Information Security Policy
- Work instruction operational security
4.1. Data Protection Management
a. Technical Measures
- Central documentation of all data protection regulations with access for employees
- Security certification according to ISO 27001
- Data protection checkpoints consistently implemented in tool-supported risk assessment
b. Organizational Measures
- Staff trained and obliged to confidentiality/data secrecy
- Regular awareness trainings at least annually
- Internal Information Security Officer appointed:
- Processes regarding information obligations according to Art 13 and 14 GDPR established
- Formalized process for requests for information from data subjects is in place
- Data protection aspects established as part of corporate risk management
- ISO 27001 certification of key parts of the company including data center operations and annual monitoring audits
4.2. Incident Response Management
a. Technical Measures
- Use of firewall and regular updating
- Use of spam filter and regular updating
- Use of virus scanner and regular updating
- Intrusion Detection System (IDS) for customer systems on order
- Intrusion Prevention System (IPS) for customer systems on order
b. Organizational Measures
- Documented process for detecting and reporting security incidents / data breaches (also with regard to reporting obligation to supervisory authority)
- Formalized procedure for handling security incidents
- Involvement of ISO in security incidents and data breaches
- Documentation of security incidents and data breaches via ticket system
- A formal process for following up on security incidents and data breaches
- Information Security Policy
- Data Protection Policy
- Work instruction operational security
- Work instruction IT user regulations
4.3. Data Protection by Design and by Default
a. Technical Measures
- No more personal data is collected than is necessary for the respective purpose
- Use of data protection-friendly default settings in standard and individual software
b. Organizational Measures
- Data Protection Policy (includes principles "privacy by design / by default")
- OWASP Secure Mobile Development Security Checks are performed
- Perimeter analysis for web applications
4.4. Order Control (outsourcing, subcontractors and order processing)
a. Technical Measures
- Monitoring of remote access by external parties, e.g. in the context of remote support
- Monitoring of subcontractors according to the principles and with the technologies according to the preceding chapters 1, 2
b. Organizational Measures
- Work instruction supplier management and supplier evaluation
- Prior review of the security measures taken by the contractor and their documentation
- Selection of the contractor under due diligence aspects (especially with regard to data protection and data security)
- Conclusion of the necessary data processing agreement on commissioned processing or EU standard contractual clauses
- Framework agreement on contractual data processing within the group of companies
- Written instructions to the contractor
- Obligation of the contractor's employees to maintain data secrecy
- Agreement on effective control rights over the contractor
- Regulation on the use of further subcontractors
- Ensuring the destruction of data after termination of the contract
- In the case of longer collaboration: ongoing review of the contractor and its level of protection
4.5. Data Processing Agreement(DPA)
forms.app has a standard Data Processing Agreement(DPA) for its users with respect to the Processing of Personal Data by us on behalf of you in connection with the forms.app Services under the Terms of Use between you and us.
Our Data Processing Agreement offers GDPR requirements, Standard Contractual Clauses and our security measures. To ensure no inconsistent or additional terms are imposed on us beyond that reflected in our standard DPA and model clauses, we cannot agree to sign customers’ DPAs.
We will not be able to redraft or add any clause to the DPA and can not sign customers’ DPAs. If you wish to sign a DPA please fill out this form.
Once we received your reply the DPA will be emailed to you and will be signed electronically by both parties.
forms.app signs confidentiality agreements with the employees and contractors. Also, all employees and contractors have a common way to report incidents approved by the organization and they will undergo at least an annual security awareness training.